Goal
Intrusion Attempt is a is a multiplayer asymmetric turn based expnadable card game with Standardized Expansion Packs where students assume the role of hackers (attackers) and corporations (defenders). The game has been envisioned as an informal supplementary tool that can be used by educators who want to convey real-world cyber attacks and defense techniques to (under)graduate students, teach about cyber crime, adversary thinking and promote security awareness in an entertaining way!
The asymmetric nature of the game and some of the game mechanics implemented in Intrusion Attempt have been influenced by games such as Android NetRunner, a discontinued collectible card game with a large fan base that takes place in a dystopian cyberpunk futuristic setup where hackers try to steal the agendas of mega-corporations.
…..[Work in progress]
Intrusion Attempt can be played in two different modes, multiplayer single-mode and multiplayer cooperative mode:
- Multiplayer single mode: in multiplayer single mode, each student selects a single role to play, namely a hacker role or a corporation role. The minimum number of participants for multiplayer single mode is two (2) (I.e. two-player mode). In two-player mode, one player selects the role of a hacker, while the other selects the role of a corporation.
For more than two (2) participants, the ratio of hackers to corporation is 1 to 2 and the recommended maximum number of participants is five (5). - Multiplayer cooperative mode: in multiplayer cooperative mode, students are allowed to play in teams no larger than two (2) participants per team. The maximum recommended number of teams is four (4).
…a bit of history
I have been working since 2017 at NTNU as research assistant for the Norwegian Cyber Range project and as a lecturer for the Ethical Hacking part of a join course called Incident Response, Ethical Hacking and Forensics (IMT3004). The penetration testing part of the IMT3004 course has a theoretical and practical approach that aims to teach students the most common techniques, methodologies and tactics used by malicious adversaries to compromise computer systems.
The course is not only popular among students with strong technical skill and abilities related to cybersecurity, it also attracts less experience students, many of which have never participated in a CTF before but are interested in understanding the technical details behind cyberattacks and may be considering pursuing a position as junior penetration testers or an executive function in cyber security.
One of the biggest challenges I faced (like most educators face in this field of expertise) is the disparity in the level of readiness and technical knowledge among the students that take the course for the first time.
The complexity of the topic, the difference in background and experiences among the students that take the course, makes teaching such a course very challenging. If this issue is left unaddressed, the level of demotivation among novice participants can grow larger as the challenges they face throughout the course will only grow in difficulty. This could eventually lead to unwanted results such as, bad scores, cheating and group collaboration when it is not allowed and a potential decline of interest of some of the novice students for the field.
Unfortunately, given the large amount of students that are allowed to take part int he course (i.e. 50+ students), it is in most cases not always possible to provide dedicated assistance to those students who are lagging behind.
One of the solutions I was eager to explore in an attempt to make the course content more engaging, more accessible and to allow students to learn without the fear of grading and judgment, was to incorporate an educative game in the classroom. To my dissatisfaction and disappointment, and even though there have been plenty of cyber security oriented games, many of them were not relevant for the course I was teaching. And those that were, did not fulfilled the objectives of the course. That is why I decided to create Intrusion Attempt.
Why a card game?
A cad game seemed very appropriate since it allows me to adjust the game to make sure that it always states true to the subject I want to gamify. This is realized by the creation of new cards and by retiring obsolete ones when needed. On top of that, the adapting/evolving nature of the game, the different options players have, and the random elements incorporated into it (in the form of e.g. event cards and dices), contributes to the uniqueness of each game play.
What is new?
Intrusion Attempt intends to differentiate itself from many card games that have been developed with a related purpose in mind by trying to achieve a level of realism that other games do not, focusing mostly on the technical side of attack and defense strategies and adversarial thinking. This make the game suitable for teaching penetration testing and red teaming.
Intrusion Attempt is meant to evolve along side with the technological advanced within this field, making it always relevant for teaching real-world offensive and defensive techniques to a mature audience.
The level of realism in Intrusion Attempt is achieved through the following elements:
1) Less abstraction
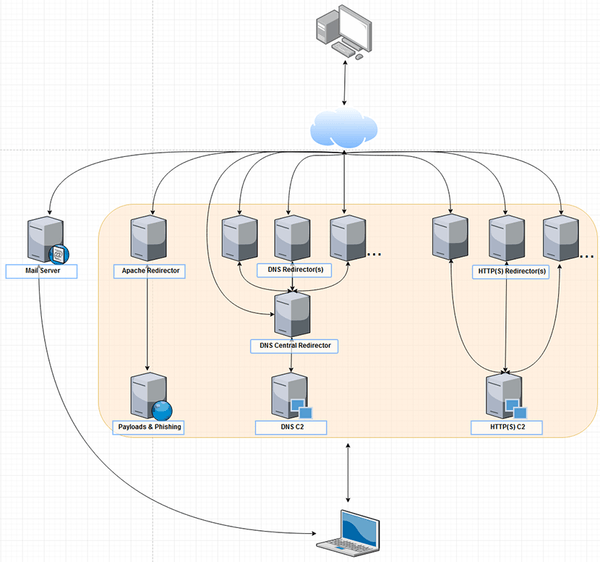
…segregate each asset based on function, why? Resilience, Agility against the blue team when campaign assets start getting detected and for scalability purposes (if one asset gets compromised, attacker should be able to re-deploy that compromised asset and not the entire infrastructure).
Abstraction plays an important role in most cyber security card games. Often, developers tend to abstract away many elements and concepts from the game to make the game less complex or to favor a particular audience. Consider for example a (spear) phishing attacking card in the game Cyber Threat Defender….
complex attacks such as spear phishing and is complex underlying infrastructure, is represented in the form of a single card.
where many of its required elements and concepts that are part of an attack are assumed to exists and are therefore abstracted away from theplayer, often in the form of a single card. This does of course favor game complexity, but it does not favor the learning process of the students.
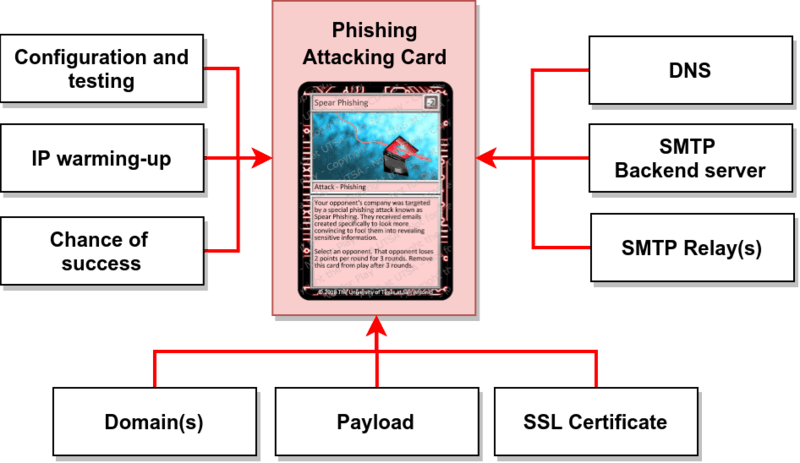
Abstraction plays an important role in most cyber security card games. Many key elements and concepts that are part of an attack are assumed to exists and are therefore abstracted away from the player, often in the form of a single card. This does of course favor game complexity, but it does not favor the learning process of the students.
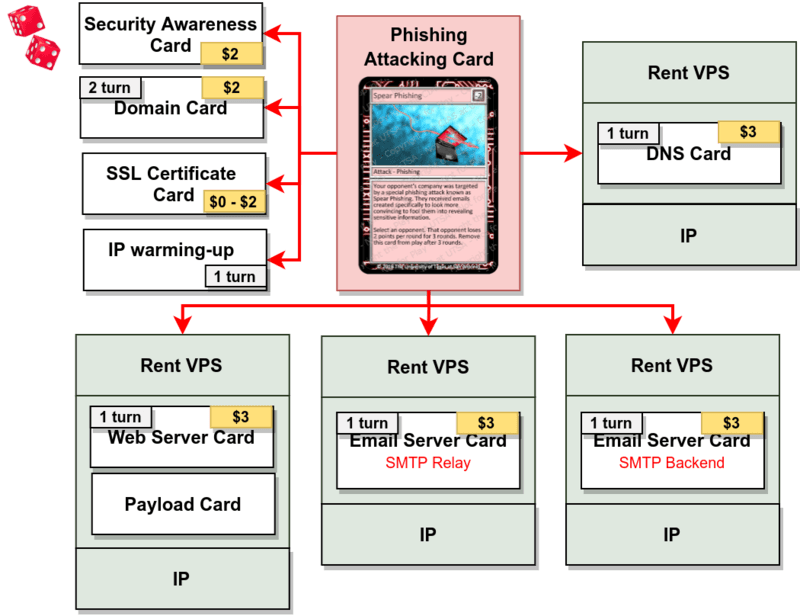
Intrusion Attempt does not abstract away important key elements from the players, they are instead playable cards that when combined together can form powerful attacks!
2) Less randomness
Randomness, luck-based mechanics = force players into new situations, make sure that players get a new opening hand each time, leading to a different experience in each match instead of the same opening plays..
unpredictability, excitement, optimize for balance. The effects of luck on player psychology and behavior are extremely relevant, especially when it comes to player retention and monetization.
In Intrusion Attempt there is no randomness when it comes to attack and defense card types! Hackers and defenders can plan and play their attack and defense strategy, respectively, from the very movement the game starts and improve upon it as the game moves forward.
Since there is no hidden information in that regard for the player,
Players can plan their attack and defense strategies as the game move forward without relying on randomness.
Randomness has been limited to the following card type: Agenda-, Campaign-, Event-, Hacker Profile– and Corporation Specific– and Personnel card types.
Many games use randomness to force players into new situations. In a collectible card game, players get different opening hands each time, leading to a different experience in each match instead of the same opening plays. Variety is very important in strategy games. Players quickly tire if they are forced to make the same moves over and over again. However, card draw—the key random mechanism that most card games use to generate variety in gameplay—has an inherent problem in that it strongly reduces realism and fairness.
https://www.gamasutra.com/blogs/ElyotGrant/20141209/231959/Removing_RNG_how_eliminating_luck_can_benefit_strategy_card_games.php
No discarding, shuffling, no randomness in drawing cards from a deck
Complete information games = Prismata, astral towers, Anachronism, Alteil, Zatch Bell
Realism is also achieved by allowing students to specialize in two specific master card decks. Cybersecurity is a complex field, in reality, people tend to specialize rather than trying to learn it all. I wanted to introduce this into the game by allowing students to specialize in a maximum of two (2) different card decks.
Relies on and refers to existing cyber security standards and frameworks such as STIX and Mitre’s ATT&CK
The introduction of identity cards into the game encourages students to role-play. Identity cards represent specific threat actors with a specific personality, motives and skills. Before the game starts, students that want to play the role of attackers, must adopt a specific hacker persona. By adopting the role of a specific threat actor, students playing the role of attackers will be able to walk in the character’s shoes and play actions that are characteristic for the type of threat actor the student is playing.
This game also introduces cyber crime vocabulary that students can learn.
Specialization is done through deck building. Before the game starts, students need to choose a maximum of two (2) card decks they want to master e.g. Malware & Reverse Engineering, Social Engineering, Wireless- , Physical- , or System and Network hacking. Limiting the amount of decks students can master, makes the game more realistic favors cooperation and encourages strategic planning.
3) Hacker Profiles
….
4) Cyber crime schemes, behaviors & DNM
The cards featured in the game have been designed to provide students with a good overview into real cyber crime activities (e.g. Business Email/Process Compromise, money mules, underground banking, corporate espionage and honey traps), generate insights into the complex world of cyber security and encourage communication, team work and understanding of the subject matter.
…….The Darknet Market (DNM) and DNM specific cards such as Escrow and Mutltisig, play an important role in the game!
…understanding cybercrime is important to be able to understand malicious actors, that is why cybercrime is included, this will make better pentesters/red teamers.
5) Interactive app & knowledge base
……
…work in progress…
